
BLOG
Russia/Ukraine Cyberwar: Healthcare Vendor Risks & Response
Published On March 4, 2022
Healthcare organizations are scrambling to adjust their cybersecurity preparation and response capabilities in the wake of potential cyberattacks stemming from the ongoing conflict between Russia and Ukraine.
CORL has been monitoring the situation closely and working with our customers and vendors to understand the extent of cybersecurity risks impacting third- and fourth-party vendor vendors servicing healthcare.
This blog post provides threat intelligence on the escalating cyberwar activities stemming from this conflict as well as recommendations for healthcare vendor risk management programs to prepare and respond to these emerging threats.
Russia-Ukraine Cyberwar Overview
According to the U.S. Cybersecurity Infrastructure and Security Agency [1], “Russia’s unprovoked attack on Ukraine, which has involved cyberattacks on Ukrainian government and critical infrastructure organizations, may impact organizations both within and beyond the region, particularly in the wake of sanctions imposed by the United States and our Allies. Every organization - large and small - must be prepared to respond to disruptive cyber activity.
Russia’s attack on Ukraine has included a barrage of cyberattacks that could potentially introduce targeted or collateral damage to many industries including healthcare. Cyberattacks stemming from this conflict are likely to impact organizations and the software supply chain both within and outside of Eastern Europe.
Healthcare entities in the U.S. are already facing a barrage of ransomware attacks stemming from Russian and Eastern European sources that specifically target healthcare organizations. Refer to the following resources for more information on these attacks:
- Podcast: Russia/Ukraine Cyberwar Preparation & Response for Healthcare
- Case Study: Ransomware Locks Up 80% of 54-Hospital Health System
- Blog Post: Your Health Held Hostage: What Ransomware Means for Patients
- Webinar Replay: Healthcare’s Response to a ‘Credible and Imminent’ Ransomware Attack
In addition to direct attacks, many of healthcare’s third-party and fourth-party vendors have assets in the region and could be impacted by the escalation of cyberattacks.
Counter-attacks from hacktivists and other enties could also escalate collateral cyber damage. The infamous hacktivist group, Anonymous, has been active in defending Ukrainian cyber assets and conducting offensive attacks against Russian assets. Another hactivist group called the Cyberpartisians has also been active in Ukraine’s cyber defense.
Healthcare enties must be vigilant in preparing and responding to cyberattacks. The following sections of this blog provide more intelligence on specific threat actors and methods as well as recommendations for healthcare organizations to prepare and respond to attacks.
Russia’s Cyberwar Capabilities & Attack Methods
Russia has launched a wide range of cyberattacks targeting Ukraine including destructive malware, DDoS, phishing, brute-force, defacement, and ransomware attacks.
Microsoft Threat Intelligence Center (MSTIC) and other threat intelligence sources have disclosed that the WhisperGate destructive malware is actively being used to target organizations in Ukraine and beyond.
The HermeticWiper malware is also in active use, which results in boot failure and renders systems inoperable. The HHS Health Sector Cybersecurity Coordination Center (HC3) urged healthcare organizations to remain on high alert due to the destructive nature of HermeticWiper malware. [2]
Recent CISA and FBI advisories have noted that “destructive malware may use popular communication tools to spread, including worms sent through email and instant messages, Trojan horses dropped from websites, and virus-infected files downloaded from peer-to-peer connections. Malware seeks to exploit existing vulnerabilities on systems for quiet and easy access.” The advisories further state that “the malware has the capability to target a large scope of systems and can execute across multiple systems throughout a network. As a result, it is important for organizations to assess their environment for atypical channels for malware delivery and/or propagation throughout their systems.” [3]
The cybersecurity firm, Mandiant, has also completed extensive and ongoing analysis of Russia’s cyberattack groups and capabilities. [4] Cyberattack groups linked to the Kremlin are designed to serve multiple functions including general espionage and offensive cyberattack capabilities. Mandiant notes that three Russian teams in particular are focused specifically on cyberattacks. These cyberattack groups are Sandworm, Temp.Isotope, and Temp.Veles.
Targeting from these Russia cyberattack groups focuses on the software supply chain (e.g. SolarWinds), strategic web compromises, and direct targeting of organizations. There are several types of attacks employed that range from gaining initial access and waiting for future exploitation of assets, wiping or destroying target systems, and deploying ransomware or fake ransomware attacks.
The CISA has also released also details about a new malware called Cyclops Blink that targets network devices and is being used by the Russian Sandworm threat actor. [5] The Cyclops Blink malware collects device information, sends it to a command and control server, and is capable of downloading and executing files, as well as pulling down more code or exploits a later time.
Some independent researchers have located web services hosting cloned copies of a number of Ukrainian government websites. For example, the main webpage of Ukraine’s Office of the President is reportedly booby-trapped with malware. [6] The cloned version of this website was modified to contain a clickable ‘Support the President’ campaign that, once clicked, downloads a package of malware to the user’s computer.
Analysis of Darknet Cyberwar Activity
A leading threat intelligence provider, DarkOwl, has provided insights and analysis into dark web discussions and data exchanges related to the Russian attack on Ukraine. [7] DarkOwl compiled and reviewed Ukraine-related data on popular deep web forums.
According to DarkOwl, several Ukrainian government networks were compromised during a series of cyberattacks in January of this year. The WhisperGate destructive malware (discussed earlier in this blog) was deployed in these instances.
Within hours of Russia’s initial cyberattacks against Ukraine in January, data described as originating from the Ukrainian government appeared on forums across the darknet and deep web.
Many of the leaked archives of data were created within a few hours of the attacks; and there are no indications they were directly obtained as a result of the January attacks.
Multiple Ukrainian government, non-profit, and Information Technology organizations experienced cyberattacks and website defacements. Attackers used a ransomware-style malware as the primary attack vector. Ominous messages were posted in Ukrainian, Polish, and Russian:
“UKRAINIANS! ALL YOUR PERSONAL DATA WAS UPLOADED TO THE INTERNET. ALL DATA ON THE COMPUTER IS BEING DESTROYED. ALL INFORMATION ABOUT YOU BECAME PUBLIC. BE AFRAID AND EXPECT THE WORST.”
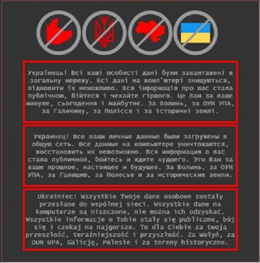 Image source: DarkOwl [8]
Image source: DarkOwl [8]
One of the leaked databases was a healthcare database called medstar.sql. Medstar is a commercial cloud-based ‘digital-medicine provider’ with telemedicine, prescription, medical imaging, and laboratory medical services in Ukraine.
Another database contained information from a mobile app with official documents of citizens, although information for only 77 individuals was made available in the dark web database.
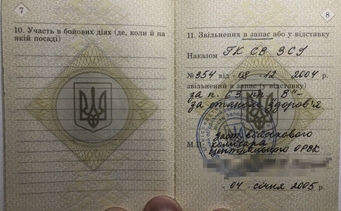 Image source: DarkOwl [9]
Image source: DarkOwl [9]
It is important to note that DarkOwl stated that “there is no evidence to conclude any of the recently shared data was sourced during the mid-January cyberattacks.” They also noted that the mid-January website defacements appeared to be a Russian-sourced false flag operation intended to incriminate Poland in the Ukraine hacks. The Polish translation used in the attack was determined to be from a non-native speaker and was likely generated with Google Translate.
It should be noted that Ukraine has officially attributed these defacement attacks to a cybercriminal group operating out of Belarus (UNC1151).
Recommendations for Healthcare CISOs and Vendor Risk Programs
The American Hospital Association (AHA) has issued guidance for healthcare organizations about the growing cyber threat from rising geopolitical tensions. AHA said that “hospitals and health systems may become incidental victims of, or collateral damage to, Russian-deployed malware or destructive ransomware that inadvertently penetrates U.S. health care entities.” [8]
As a result, healthcare organizations must heighten alerts and preparations for attacks on their infrastructure and supporting IT systems and applications. Healthcare entities must also defend against risks associated with third-party vendors and the software supply chain.
Gather Information on Offshore Vendors
The first step in preparing and responding to the Russian cyber threat is to identify which of your third- and fourth-party vendors have assets or an IT presence in Ukraine or Russia.
This can be accomplished by leveraging CORL’s vendor risk intelligence data along with other geo-tagging asset technologies like Black Kite.
Review Assessment Archives & Update Vendor Inventories
Healthcare VRM program managers should update inventories to flag any vendors with a direct presence or fourth-party assets in Russia or Ukraine. Any vendors in those regions should also be reviewed for any prior risk assessment activity to determine which vendors may have greater exposure to the threat vectors outlined earlier in this blog.
Vendors with a presence in Russia or Ukraine should also be prioritized based on criticality and compliance risk exposures following standard vendor tiering models.
Organizations should also review historical risk assessment results for vendors that meet the criteria above. Reviews should focus on the vendors’ security control capabilities for the following domains associated with the Russia/Ukraine situation including:
- Patching
- Incident response
- Business continuity
- Disaster recovery
- Logging and monitoring
- Network controls & segmentation
- Cloud configurations
- Endpoint protections
- Multifactor Authentication (MFA)
Establish a Communication Plan
Healthcare VRM program managers and CISOs should confirm points of contact for vendors and internal business stakeholders for any vendors meeting the criteria described above.
It is important to also identify communication escalation paths with vendors in the event that the ongoing cyber conflict impacts your vendors in any material way.
Reach Out to Riskiest Vendors
It is important to recognize that vendors with assets Eastern Europe have their hands full responding to the cyber situation on the ground. CORL does not recommend issuing full scale and scope risk assessments of impacted vendors. Instead, we recommend reaching out to vendors with the following approach:
- Request vendor’s action plan on Russia/Ukraine response and contact info
- Encourage vendors to maintain backup copies of data outside the region
- Identify which products/solutions are impacted (and compare that to your inventory and products deployed in your environment)
- Encourage vendors to maintain backup copies of data and store those copies outside of Eastern Europe
- Focus any follow up conversations or information collection around the key domains associated with the latest attacks including patching, incident response, BC/DR, logging and monitoring, network segmentation, cloud security, endpoint protections, and MFA
Track Vendor Remediation and Corrective Action
VRM programs should focus vendor remediation attention on key domains associated with Russian cyberattacks that are listed above.
It is also advisable to have a “Plan B” for vendors with critical assets or leadership in Russia or Ukraine. It may be worth exploring alternative vendors if they have Russian ownership as a backup in case economic sanctions impact the vendor’s viability or finances.
Guidance from the CISA, FBI, & NSA
The U.S. federal government has issued a series of guidance materials to help organizations prepare and defend against rising cyberattacks during this conflict. The guidance is aimed at reducing the likelihood of a damaging cyber intrusion. [9]
This guidance should be applied to healthcare organizations and used as a guide for conversations with third-party and fourth-party vendors for areas to focus energy in the near term.
Specific recommendations for healthcare entities and vendors include:
- Validate MFA is in place for remote and privileged access
- Ensure software is up to date
- Disable unnecessary ports and protocols
- Validate cloud security configurations are aligned with industry best practices
The CISA also recommends taking steps to quickly detect a potential intrusion including:
- Enabling logging
- Focusing cybersecurity and IT personnel on monitoring activities
- Confirming anti-malware software is applied across all systems
- Monitoring and inspecting any traffic coming from Russia or Ukraine and reviewing access controls for any related traffic
Guidance also includes ensuring that the organization is prepared to respond if an intrusion occurs including:
- Designating a crisis response team
- Identifying points of contact for technology, communications, legal, and business continuity resources
- Ensuring availability of staff and providing a means to handle surge support for incident response
- Conducting routine tabletop exercise
The CISA has also weighed in on ways that healthcare entities can maximize the organization's resilience to a destructive cyber incident including testing backup procedures for critical data and systems and isolating backups from network connections.
The U.S. federal government urges CEOs and leaders to empower Chief Information Security Officers during this crisis. Organizations are advised to lower reporting thresholds to identify, capture, and respond to attacks or abnormal network activity. Healthcare organizations are further advised to focus on business continuity processes and capabilities and to “plan for the worst”.
The CISA has also issued an alert to specifically protect against destructive malware like the WhisperGate and HermeticWiper malware used in Russia’s latest attacks against Ukrainian assets. [10]
Recommendations from the CISA’s alert AA22-057A: Destructive Malware Targeting Organizations in Ukraine includes recommendations to:
- Establish network segmentation and ACLs
- Put network and storage devices on restricted VLANs
- Require Multi-factor Authentication (MFA) for remote and privileged access
- Restrict the “Everyone”, “Domain Users”, and “Authenticated Users” groups
- Restrict service accounts including denying access to network shares and prohibiting local or interactive logons
- Log and monitor network flow, detect port scanning, and detect network configuration changes
- Stagger automated patching schedules in case patching deployment systems get hijacked
- Harden systems with patching, scanning, and best practice OS configurations
- Perform a Business Impact Analysis (BIA)
Conclusion
Cyberattacks stemming from the Russian invasion of Ukraine are likely to continue for some time as the conflict escalates and evolves into the summer and beyond.
Healthcare organizations and their vendors must continue to make proactive investments in cybersecurity defense and response capabilities. Organizations must maintain a heightened state of readiness to combat the growing threats of ransomware and the potential for escalations in cyberwarfare in the months ahead.
CORL will continue to monitor the situation in Ukraine and provide guidance and resources for the healthcare industry and vendor risk management programs as this crisis evolves.
Contact our team if you have any questions or to learn more about our managed services and next generation exchange for healthcare vendor risk data that gets results and lowers third-party vendor risks.