BlogTPRM
Top 10 Healthcare Supplier Risk Management Challenges Facing Providers in 2025
3 Minute Read
Read Top 10 Healthcare Supplier Risk Management Challenges Facing Providers in 2025TPRM
By CORL Technologies | June 19, 2024
As we approach the end of Q2 and enter Q3, organizations that sell products and services to healthcare are feeling the burn. The burden of security questionnaire response typically peaks mid-year and its ugly impact on the healthcare sales cycle manifests in the forecast. Meanwhile, buried under a litany of security assessments, many cybersecurity teams have time for little more than questionnaire response. Critical initiatives to reduce cyber risk are necessarily put on the back burner as internal stakeholders ‘take a number’ and external bad actors take note.
A recent study by the Ponemon Institute, surveying over 600 IT security professionals, found that third parties spend over 15,000 hours annually on these assessments. The same study indicates that current assessment workflows aren’t working for anyone. Despite intensive vendor effort, 54% of enterprises reported that the assessment data they receive is not valuable. This discrepancy between workload and relevance is more than inefficiency and monotony. It is a threat to vendor-client trust.
The reason for this discrepancy is that assessments, as they currently stand, do little to reduce third-party risk; only vendor IT teams can do that. And with questionnaires claiming the most significant portion of limited vendor IT resources, the need for a better and faster way is not a ‘nice to have’ but an absolute necessity to reduce cyber risk ecosystem-wide.
Vendors selling to hospitals require cyber security assessment tools that transform the process and virtually eliminate the burden of responding to security questionnaires to streamline the assessment process, accelerate the sales cycle, and save time and money for more meaningful cyber risk reduction. It’s important to choose a solution that moves beyond passive response reuse to measurably enhance both speed and response quality at scale. But in a noisy space where ‘me too’ messaging abounds, it can be challenging to identify the right one.
In this blog, we will explore several critical indicators of an effective questionnaire solution–one that not only accelerates the assessment process but also ensures that questionnaire responses are meaningful and strengthen vendor-client trust. Read on to discover how the right cyber security assessment tool can empower you to enhance credibility, improve sales velocity, increase win rates, and dedicate more IT focus to the things that matter most. If you are a sales professional, IT leader, or legal professional at an organization that sells products or services to healthcare, read on. This article was written for you. If you are a healthcare organization who happened upon this blog post, consider forwarding the link to your vendors and business associates. Your stakeholders and your cybersecurity team will thank you.
The current state of security questionnaires
Before we can characterize a proper solution for vendor security questionnaire response, we need to unpack why the current approach isn’t working. Vendor security questionnaires have long been an integral part of the healthcare industry’s third-party risk management (TPRM) processes. They are designed to assess the vendors’ security posture and ensure they comply with stringent healthcare regulations and standards.
While vendors never met these questionnaires with open arms, they have become increasingly burdensome, and here’s why.
Increasing length paired with lack of standardization
Ask anyone in the industry and they’ll tell you security questionnaires always seem to be getting longer, often ballooning to hundreds of questions and controls. As the technological landscape becomes more complex and cyber threats become more formidable, the length problem only intensifies. What’s more is that each healthcare client has its own unique set of requirements, which leads to a lack of standardization across questionnaires. Even the same questions are often asked differently, making it impossible for vendors to reuse responses from one questionnaire to the next. Both realities lead us to our next major shortcoming.
Monopolization of IT resources
For organizations providing products and services to healthcare, the IT function has never been more vital to success. As the chief executor of initiatives that advance innovation in the business and lower risk for the organization, IT has no shortage of critical priorities. And yet, assessment response most often falls to IT teams, diverting their attention from other critical tasks. This monopolization of resources not only leads to delayed responses; it leaves the organization at risk. That is the ultimate irony of manual assessment response.
Slow sales cycles and low client trust
The healthcare sales cycle is far from an example of efficiency—even without the security assessment. But with the average security questionnaire response taking xx days, security assessments are a leading sales bottleneck. That is 15,000 hours added to the sales cycle. Aside from their inherent threat to sales forecasts everywhere, security assessments bury meaningful client relationships under layers of procedure and make it exceedingly challenging for vendors to prove they are worthy of trust. Sluggish submissions and poor response quality may erode prospective clients’ confidence in the vendor’s ability to respond to their questions or concerns quickly and decisively.
What to look for in a security questionnaire solution for healthcare
Now that we have our arms around the problem, let’s surface some key features for a proper solution. Before we dive in, recall that cybersecurity in healthcare is a specialized function that demands specialized expertise in healthcare vendor relationships, regulations, policies, and threats. Sector-agnostic tools that are integrated into RFP generators possess none of these, so they naturally aren’t well-suited to solve the security assessment problem in healthcare.
A dedicated focus on healthcare cybersecurity is, therefore, a critical starting point for your solution search, and table stakes for a solution that can address your needs. But what else? What features should a proper security questionnaire response tool deliver?
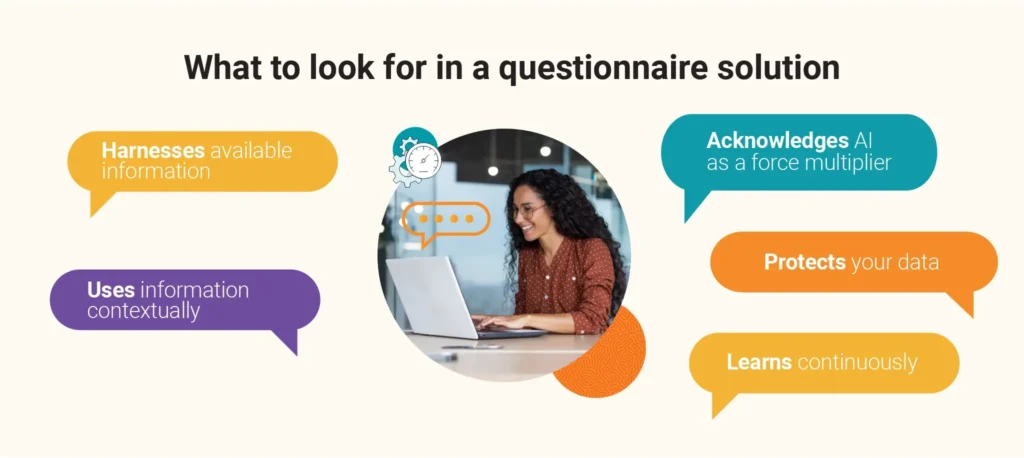
Ability to harness all available information
First, the right solution should look beyond prior questionnaire responses, embracing the wealth of information your organization already has available rather than forcing you to generate even more. The reality is that many healthcare vendors already have the information they need to respond to questionnaires residing in their existing documentation. Penetration tests, security risk assessments, HITRUST certifications, SOC 2 reports—all of these include tremendous insight that can expedite and enhance questionnaire response.
Contextual use of information
To move beyond passive response reuse, context is key. Drawing upon your profile data, prior responses, and previous documentation, your cybersecurity assessment tool should apply information contextually rather than literally. Building upon a strong understanding of healthcare cybersecurity, the right solution will understand question intent and tailor responses accordingly. Context-rich responses demonstrate a deeper understanding of the client’s requirements, enhancing your credibility and response quality while also saving extensive time and resources.
Continuous learning
While an effective solution will prioritize quality first in its responses from the start, it should only get better and more knowledgeable over time. As you continue to use the solution and refine its responses with your own input and insights, it should take note. Its responses will naturally become more and more aligned with yours over time, manifesting in an enhanced percentage of matched questions, fewer edit rounds, and less time.
AI as a force multiplier
While harnessing AI can greatly enhance the efficiency and accuracy of questionnaire responses, it should be embraced as an enabler and not a panacea. Look for a solution that provides the people in addition to the product—offering hands-on support to support you in managed assessment response where needed and even more importantly, cybersecurity risk reduction and compliance. AI on its own is powerful, but AI with the right partner is truly transformative.
Proprietary AI model for data protection
The healthcare industry is abuzz with talk of AI’s potential impact—but in addition to new possibilities, ML and AI models also introduce new risks. By choosing a solution with a proprietary, closed AI model that is securely hosted within the provider’s infrastructure, vendors can ensure the protection of their organization’s sensitive information. Data should be encrypted in transit and robust end user controls should limit points of access.
Introducing CORL Companion: your assistant for rapid security assessment response
With each manual assessment response comes an associated impact on sales, profitability, and risk. CORL Companion transforms this process by bringing automation and efficiency to security assessment response. This empowers vendors to spend less time on repetitive tasks and more time on what really matters—the growth and security of their organizations.
Using a secure, cybersecurity-specialized AI engine, CORL Companion generates meaningful, high-quality responses for stakeholders to quickly review, refine, and submit. It transcends passive question reuse by harnessing profile data, past assessments, assurances, evidence, and other documentation to create tailored responses that enhance credibility and trust.
By integrating AI with CORL’s hands-on support, CORL Companion ensures that healthcare vendors meet the rigorous demands of security assessments while continually advancing their cybersecurity posture over time.
Are you ready to reclaim more time for sales and cybersecurity? Speak to a member of our team about how you can bring CORL Companion to your organization today.
 CORL Technologies
CORL Technologies
CORL transforms TPRM chaos into clarity
CORL is a leading provider of vendor risk management solutions for the healthcare industry. CORL gets results by scaling organizational and vendor risk programs through our healthcare vendor risk clearinghouse solution, dashboard reporting that business owners can understand, and proven workflows that drive measurable risk reduction. CORL accelerates the speed of vendor risk assessments and holds vendors accountable for remediating risk exposures.
Related Posts
BlogTPRM
By CORL Technologies | August 14, 2025
3 Minute Read
Read Top 10 Healthcare Supplier Risk Management Challenges Facing Providers in 2025BlogCompliance
By CORL Technologies | June 24, 2025
5 Minute Read
Read Unlocking Vendor Assurance: A Deep Dive into CORL Technologies’ Assessment Suite
BlogTPRM
By CORL Technologies | May 19, 2025
2 Minute Read
Read More Than a Checkbox: Why Right-Sizing Vendor Risk Remediation Is the Key to Smarter TPRM
Webinars
WEBINAR H3PT Presents: Operationalizing TPRM for Success Join us for a focused, real-world conversation with healthcare security and risk leaders tackling today’s most pressing TPRM challenges. This session will bring together a small panel of experts for an insightful discussion on how to strengthen third-party risk programs in an evolving threat landscape. This won’t be […]